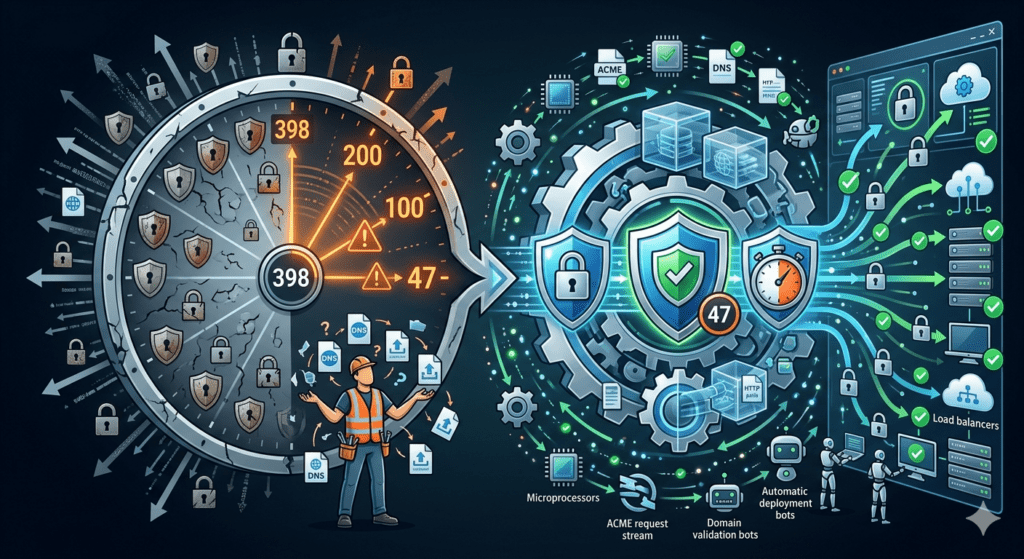
The SAN Certificate Complexity Trap: Navigating the 47-Day Validity Window
Enterprises must fundamentally change their approach to SAN certificate management as the industry moves toward a 47-day maximum validity period. Historically, Subject Alternative Name (SAN) configurations allowed administrators to secure multiple domains under a single umbrella, which simplified licensing. However, as the industry forces the certificate lifecycle into a high-velocity cycle, maintaining multi-domain TLS agility becomes an immense operational burden. Consequently, organizations must pivot toward automation to prevent the inevitable outages caused by manual configuration errors in these complex, multi-domain environments.
Strategic Pillars of Multi-Domain TLS Agility
To survive the transition to shorter validity periods, IT leaders must rethink how they architect and deploy multi-domain credentials across four core areas.
1. Scaling Beyond Manual Validation Latency
The most significant bottleneck in SAN certificate management involves Domain Control Validation (DCV). When a certificate contains multiple SANs, the Certificate Authority requires proof of ownership for every single domain listed. In a manual environment, this requires an admin to coordinate DNS changes or file uploads for dozens of endpoints simultaneously.
If you miss the validation window for just one domain on a SAN list, the CA will block the issuance of the entire certificate. Therefore, you must automate the validation path. Specifically, your infrastructure needs a reliable, programmatic way to respond to DCV challenges without human intervention. This shift ensures that your multi-domain TLS agility remains high, even as the industry shrinks validation reuse windows to just ten days.
2. Standardizing Policy Enforcement for Complex Identities
Multi-domain certificates often become “catch-all” buckets for various departments, leading to a loss of security standardization. One team might require an RSA 2048-bit key, while another demands ECC for better performance on mobile devices. When these requirements clash within a single SAN certificate, the result is often a “lowest common denominator” security posture that leaves the enterprise vulnerable.
Achieving true multi-domain TLS agility requires the strict enforcement of cryptographic policies at the moment of request. You must ensure that every SAN certificate—regardless of how many domains it covers—meets your organization’s highest security standards. Specifically, your system should enforce uniform key lengths and algorithms across all listed identities. By automating this enforcement, you eliminate the “shadow PKI” risks that occur when individual teams create their own non-standard configurations.
3. Orchestrating the “Last Mile” of Multi-Platform Deployment
A SAN certificate is only useful if it is correctly installed across every endpoint it represents. In many cases, this means the same certificate must reside on load balancers, web servers, and API gateways across different geographical regions. When the validity period drops to 47 days, the manual deployment of these files becomes an impossible task.
The gap between issuance and installation serves as a primary cause of certificate-related outages. Specifically, if a renewal is successful but the installation fails on just one of the five servers using that SAN, the service will break for users hitting that specific node. Therefore, your SAN certificate management strategy must include end-to-end orchestration. You need a pipeline that pushes the renewed credential and reloads the necessary services across the entire infrastructure automatically.
4. Mitigating the Risk of Configuration Drift
As the certificate lifecycle accelerates, the risk of configuration drift increases. Over time, domains are added or removed from a SAN list, and server paths change. In a manual world, keeping these records accurate is a losing battle. Consequently, your PKI becomes a collection of “best guesses” rather than a source of truth.
To maintain continuous availability, you must move toward a model where the system handles the enrollment and renewal based on pre-defined templates. This ensures that every renewal is an exact, policy-compliant replica of the previous state—unless a deliberate change is made. By removing the variability of human “copy-paste” errors, you guarantee that your multi-domain identities remain consistent and secure throughout their shortened lifespans.
How CertAccord Enterprise Optimizes SAN Workflows
CertAccord Enterprise provides the discipline and automation required to master complex certificate identities. We help organizations solve the “how” of the certificate lifecycle, ensuring that multi-domain assets move from issuance to installation without friction.
Enforcing Policy-Based SAN Certificate Management
CertAccord Enterprise acts as the central policy engine for your certificate requests. Instead of allowing ad-hoc SAN configurations, our platform ensures that every multi-domain request follows your defined security rules. Specifically, the system enforces these standards across Linux and Windows environments. This ensures that every identity—no matter how many subdomains it contains—adheres to your organization’s cryptographic requirements every single time.
Driving Multi-Domain TLS Agility Through Automation
By automating the routine tasks of enrollment and renewal, CertAccord Enterprise removes the heavy lifting from your IT staff. It manages the entire request and installation path, ensuring that renewed SAN certificates reach their destination servers seamlessly. Therefore, your engineers no longer need to manually coordinate complex multi-domain updates every six weeks. This reduction in manual effort allows your team to focus on high-level security architecture while protecting your infrastructure from the risks of manual error.
Final Thoughts
The 47-day window is a fundamental challenge to how enterprises handle multi-domain trust. SAN certificate management is no longer a task that can be handled through administrative spreadsheets or manual oversight.
By embracing automated enforcement and strict policy standards today, you ensure that your organization remains agile in the face of rapid industry shifts. CertAccord Enterprise provides the structure you need to automate these high-velocity workflows and maintain total control over your digital identities. Consequently, you can secure your multi-domain infrastructure without increasing your operational burden.
