The Great Inflection: Transitioning to Cryptographic Automation
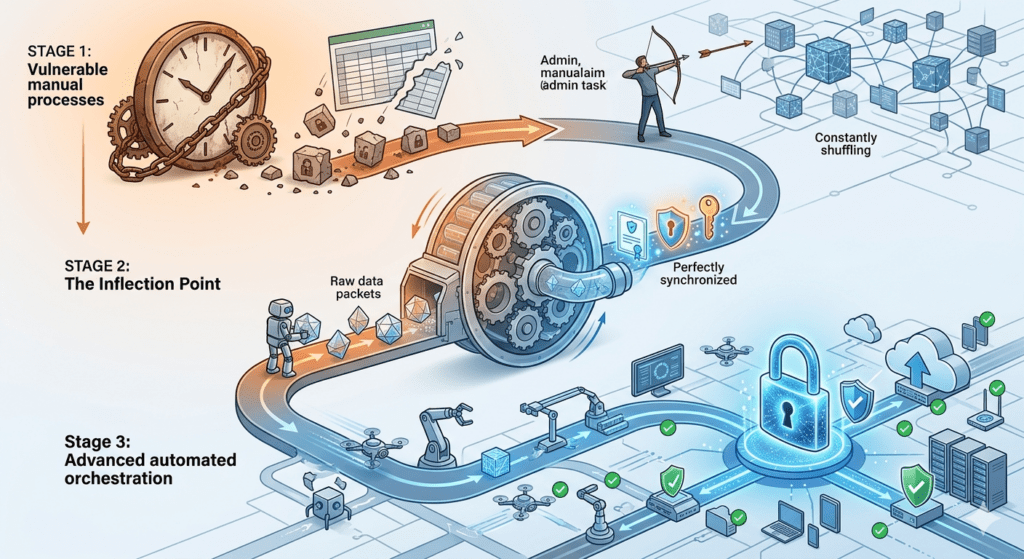
The digital landscape has officially reached an inflection point where traditional certificate management methods no longer suffice. For years, IT departments treated digital certificates as static assets—identities you could manage with a spreadsheet and a calendar reminder. However, the modern enterprise network has evolved into a high-velocity environment of short-lived cloud instances and microservices. Consequently, organizations must pivot toward cryptographic automation to maintain stability.
Moving beyond manual processes is no longer just a matter of convenience. Instead, it represents a necessary shift in certificate lifecycle maturity. As the industry shortens validity periods and introduces complex quantum-resistant algorithms, the sheer volume of cryptographic tasks will overwhelm even the most diligent security teams. To survive this shift, enterprises must stop “managing” certificates and start “orchestrating” them through policy-driven enforcement.
Scaling Beyond the Limits of Human Oversight
In the past, a security engineer could manually handle a few dozen certificate renewals each month. Specifically, they would generate a CSR, submit it to the CA, and manually install the resulting file. Today, however, the volume of internal and external certificates has exploded.
If you continue to rely on human intervention for these routine tasks, you introduce a massive margin for error. Manual processes are inherently slow and prone to oversight, which leads to expired certificates and production outages. Therefore, cryptographic automation must take over the heavy lifting. By removing the human element from the issuance and installation path, you ensure that your security staff can focus on high-level architecture rather than repetitive maintenance.
Establishing Standardization and Certificate Lifecycle Maturity
Standardization acts as the bedrock of a secure PKI. Without a centralized policy, different teams within the same organization often use varying key lengths or weak signing algorithms. This fragmentation creates a “shadow PKI” that becomes nearly impossible to defend during a security audit.
Achieving higher certificate lifecycle maturity requires the strict enforcement of cryptographic standards at the point of issuance. You must mandate that every certificate—whether it secures a Linux server or a Windows application—follows a uniform set of rules. Specifically, these rules should dictate the allowed Certificate Authorities and key types. When you enforce these standards through cryptographic automation, you eliminate configuration drift and ensure that every identity in your network remains “secure by design.”
Bridging the Gap Between Issuance and Installation
A common failure point in the certificate lifecycle occurs during the “last mile” of deployment. Many organizations successfully automate the request for a certificate but still require an admin to manually bind that certificate to a service.
This gap between the Certificate Authority and the endpoint represents a significant operational risk. If a certificate is issued but never correctly installed, the service will eventually fail. Consequently, your cryptographic automation strategy must include the end-to-end orchestration of the certificate’s journey. You need a reliable path that pushes the credential directly to the server and reloads the necessary services without manual touchpoints. This level of orchestration ensures that your handshake between systems never breaks.
Preparing for High-Velocity Certificate Lifecycle Maturity
The industry is currently facing several rapid transitions, including the move toward 47-day certificate validity and the looming threat of “Q-Day.” These changes require organizations to be “crypto-agile”—meaning they can rotate their entire certificate inventory at a moment’s notice.
If your PKI relies on manual scripts, you cannot achieve this level of agility. Instead, you must build a foundation where you can update a global policy and have that change propagate across the enterprise automatically. This preparation is a hallmark of high certificate lifecycle maturity. Specifically, it allows your organization to respond to new threats or industry mandates with speed and precision, rather than reacting with emergency “fire drills.”
How CertAccord Enterprise Drives Cryptographic Automation
CertAccord Enterprise provides the enforcement layer required to navigate this industry shift. We help organizations move away from reactive maintenance and toward a proactive, automated infrastructure.
Enforcing Policy-Based Workflows
CertAccord Enterprise acts as the “policy engine” for your PKI. Instead of allowing ad-hoc certificate requests, our platform ensures that every request follows your defined security standards. Specifically, the system enforces these rules across your entire environment, including Linux, Mac and Windows systems. This ensures that every identity follows your organization’s cryptographic requirements every single time, providing a consistent security posture.
Advancing Security Through Automated Enforcement
By automating the routine tasks of enrollment and renewal, CertAccord Enterprise removes the operational burden from your IT department. It focuses on the “how” of the certificate lifecycle—ensuring that the request, issuance, and installation happen seamlessly in the background. Therefore, your engineers no longer need to spend days every month on certificate housekeeping. This reduction in manual effort allows your team to reach a higher level of certificate lifecycle maturity while protecting your infrastructure from the risks of manual error.
Final Thoughts
The inflection point in certificate management is a call to action for enterprise security leaders. Cryptographic automation is no longer an optional upgrade; it is the fundamental requirement for a secure, scalable network.
By embracing automated enforcement and strict policy standards today, you ensure that your organization can handle the high-velocity demands of the future. CertAccord Enterprise provides the structure you need to automate these workflows and maintain total control over your cryptographic assets. Consequently, you can secure your digital identities without increasing your operational burden.
