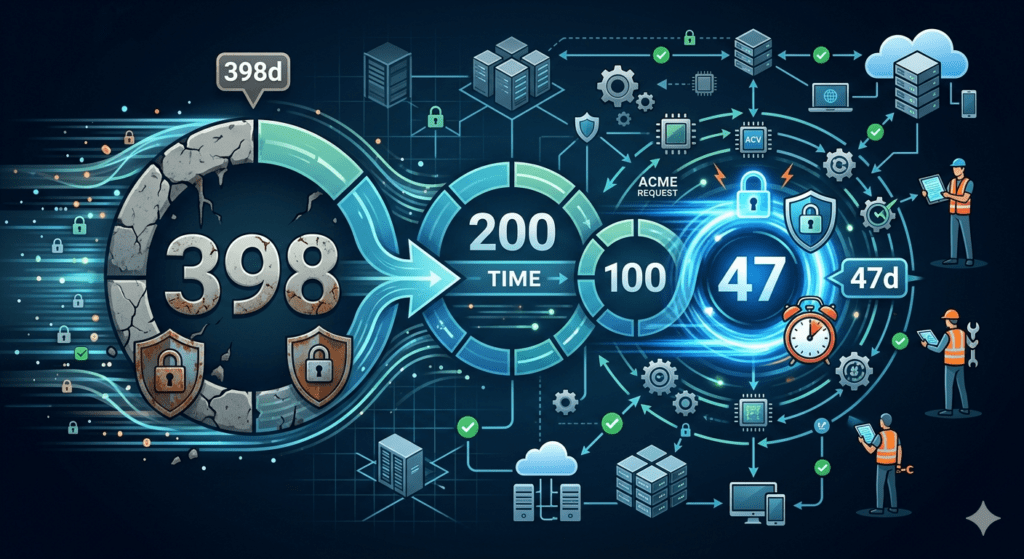
The industry is currently undergoing a massive shift in how public trust works. Driven by Google’s roadmap and the CA/Browser Forum, the maximum allowed certificate expiration time for public TLS certificates is shrinking rapidly. Industry leaders plan to reduce this window in stages until it hits just 47 days by March 2029.
This change is not just a minor policy update; it represents an operational sea-change for every IT department. Consequently, the TLS certificate lifecycle is transforming from a seasonal maintenance task into a high-velocity, continuous process. For enterprises, this means the “manual” way of managing trust is officially reaching its end of life.
Navigating the Industry Roadmap to 2029
The industry is reducing the certificate expiration time in deliberate stages to force a transition toward “crypto-agility.” Each phase forces organizations to adopt automation before the final 47-day limit becomes mandatory.
| Effective Date | Maximum Validity Period | Impact on Organizations |
| Sept 1, 2020 (Current) | 398 Days | Standard ~13-month renewal cycle. |
| March 15, 2026 | 200 Days | Renewal frequency nearly doubles; manual tracking begins to fail. |
| March 15, 2027 | 100 Days | Maximum 3-month lifespan; automation becomes a requirement. |
| March 15, 2029 | 47 Days | Final target; certificates are treated as ephemeral assets. |
As these windows shrink, the “safety buffer” IT teams once enjoyed disappears completely. Previously, a one-year certificate provided a massive cushion for renewal errors. At 47 days, however, a single failed renewal attempt will lead to a production outage in a matter of hours. Because the volume of work will increase eightfold, teams can no longer keep pace without a structured, repeatable enforcement strategy.
Managing Shorter Windows for the TLS Certificate Lifecycle
One of the most overlooked aspects of this shift involves the reduction in Domain Control Validation (DCV) reuse periods. Historically, once you proved you owned a domain, that proof stayed valid for up to 398 days. Under the new rules, this validation window will also shrink until it reaches just 10 days by 2029.
This change means your TLS certificate lifecycle now links directly to your validation infrastructure. If your method of proving domain ownership (such as a DNS record or a file-based challenge) fails, you have an incredibly narrow window to fix the issue before the Certificate Authority blocks issuance. For enterprises, this means validation can no longer be a background step. Instead, it must become an integrated, automated part of the certificate request process that executes flawlessly every few weeks. Furthermore, any friction in the validation chain now creates an immediate risk to service availability.
Addressing the Deployment Bottleneck in PKI
Frequent renewals put immense pressure on deployment infrastructure. Obtaining a certificate from a CA is only the first half of the battle. Specifically, the second half requires you to ensure the new certificate installs correctly across every endpoint, from load balancers to internal application servers.
In a 47-day cycle, the risk of a “successful renewal but failed deployment” rises sharply. If your deployment process remains manual, you risk a “split-state” scenario where some nodes serve the new certificate while others serve an expired one. This fragmentation causes intermittent connection errors that are notoriously difficult to troubleshoot. Because the renewal cycle will move so fast, automation must bridge the gap between the CA and the final application. Reliability now depends on the ability to push new credentials to thousands of endpoints without a single manual touchpoint.
How CertAccord Enterprise Secures the TLS Certificate Lifecycle
As the industry forces a 47-day certificate expiration time, organizations must move away from ad-hoc scripts. CertAccord Enterprise by Revocent provides the discipline required to navigate this transition smoothly by focusing on workflow enforcement.
Enforcing Policy and PKI Efficiency
CertAccord Enterprise focuses on the “enforcement” side of PKI. Instead of hoping that every admin follows the right steps, our platform ensures that every certificate request follows a strictly defined, policy-based workflow. Furthermore, this ensures that every certificate uses the correct cryptographic parameters, such as RSA-4096 or ECC, every single time. As renewal frequency increases, this level of consistency provides the only way to prevent configuration drift across the enterprise.
Automating the Certificate Expiration Time Transition
The platform removes the human element from the most dangerous part of the process: the installation. CertAccord Enterprise automates the end-to-end process of requesting, receiving, and installing certificates across Windows, Linux, and macOS environments. By making the TLS certificate lifecycle predictable and repeatable, it eliminates the variability that leads to outages. In a world of 47-day certificates, you do not need a tool that just sends alerts; you need a system that ensures the new certificate is already in place and the service has been successfully reloaded.
Final Thoughts
The shift to a 47-day certificate expiration time marks the end of “set-and-forget” security. It demands a higher level of operational maturity where teams treat certificates as ephemeral assets rather than permanent fixtures.
The TLS certificate lifecycle has become a core operational metric for reliability and availability. Organizations that embrace structured, policy-driven automation today will handle the 2029 deadline as a non-event. Conversely, those that wait may find themselves overwhelmed by a cycle of constant manual renewals and avoidable outages.
