How CertAccord Enterprise Works
Automate Microsoft ADCS or GlobalSign certificate creation and renewal across your network
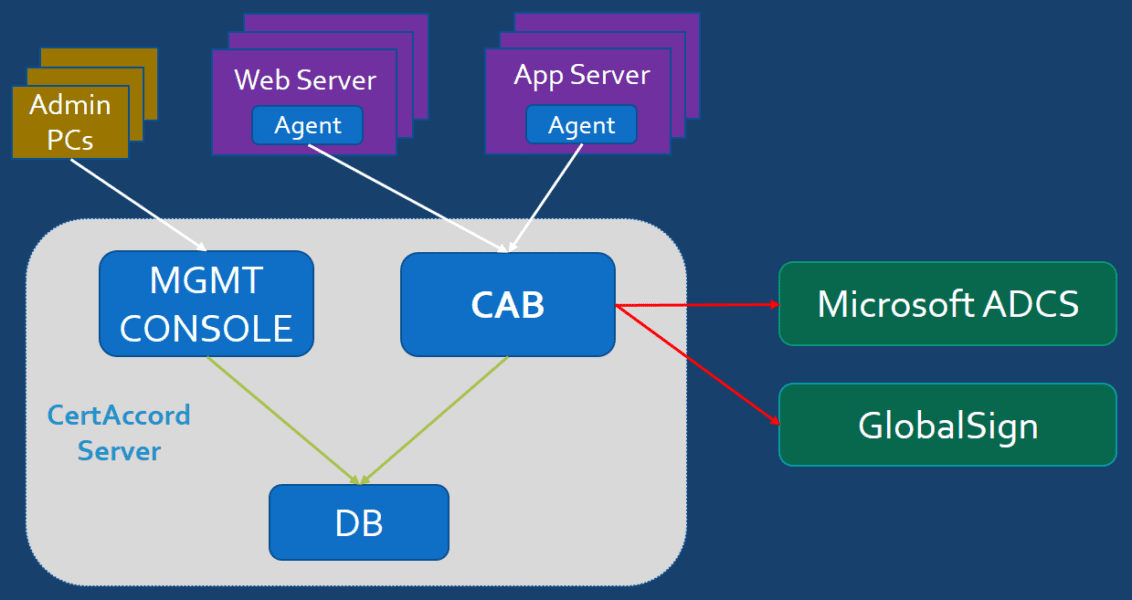
CertAccord Enterprise consists of a Server and an Agent component. The Server communicates with one or more Certificate Authority (CA) products such as Microsoft ADCS using native APIs. Agent software is installed on each end-node device (e.g. Web Servers, Application Servers, etc) on which certificates will be installed and managed.
The Server runs on Microsoft Windows Server 2012 (or later) and is typically installed on-premise on a physical or virtual machine (VM) guest.
The Server consists of three sub-components:
- Product Database (DB). A Microsoft SQL Server database installed locally on the Server or on a different network accessible server supplied by the customer.
- Certificate Authority Bridge (CAB). Integrates and communicates with CAs. Communicates and controls Agents.
- Management Console (MGMT CONSOLE). Web based GUI which is typically used by CertAccord product admins to configure the product.
The end-node computer running the CertAccord Agent communicate with a CertAccord Server using a REST API. The Agents never communicate directly with any CA or any other Microsoft infrastructure service. This greatly simplifies the installation of CertAccord since you do not have to create or manage the end-nodes in Active Directory.
The Agent has a "daemon" ("service" process) which starts automatically at system boot. The Agent daemon is responsible for checking in with a Server to look for updated policy and configurations. It is also responsible for checking and performing automatic renewals of certificates.
An IT System Administrator (admin) can also run the Agent's Command Line Interface (CLI) to quickly and simply request a new certificate or perform other tasks. Certificate creation is as simple as running:
cmbagent cert create purpose=webserver
The Agent automates the generation of a local private key using policy data obtained from a Server. It generates a CSR and signs it, then sends the CSR to a Server and waits for a response. Once the response is received, the new certificate is stored on the local file-system.
Contact Revocent
✆ +1-408-638-9323
✉ [email protected]
